Cybersecurity experts have uncovered a covert botnet engineered specifically to conduct distributed denial-of-service (DDoS) attacks.
Known as Masjesu, the botnet has been promoted on Telegram as a DDoS-for-hire service since its emergence in 2023. It is designed to compromise a broad spectrum of Internet of Things (IoT) devices including routers and network gateways across multiple hardware architectures.
“Masjesu is engineered for persistence and minimal visibility, prioritizing cautious and discreet execution rather than mass propagation,” said Trellix security researcher Mohideen Abdul Khader F in a report released Tuesday. “To ensure its longevity, it intentionally steers clear of blocklisted IP ranges, including those associated with the U.S. Department of Defense (DoD).”
The service is also referred to as XorBot, a name derived from its use of XOR-based encryption to obfuscate strings, configuration files, and payloads. Chinese cybersecurity firm NSFOCUS first documented the malware in December 2023, attributing its operation to an individual using the alias “synmaestro.”
An updated version of the botnet identified approximately one year later introduced 12 additional command-injection and remote code-execution exploits. These new capabilities enable attacks against routers, cameras, DVRs, and NVRs produced by vendors such as D-Link, Eir, GPON, Huawei, Intelbras, MVPower, NETGEAR, TP-Link, and Vacron, significantly expanding its initial access techniques. The update also included new modules dedicated to launching DDoS flooding attacks.
“XorBot represents a rapidly evolving botnet family with strong growth potential, continuously infecting and controlling new IoT devices,” NSFOCUS noted in November 2024. “Its operators are increasingly leveraging social media platforms especially Telegram as primary channels for recruitment and marketing, actively promoting their services to establish a foundation for sustained expansion.”
Recent research from Trellix indicates that Masjesu actively markets its ability to execute large-scale volumetric DDoS attacks, highlighting its extensive and diverse botnet infrastructure. The service is positioned as suitable for targeting content delivery networks (CDNs), gaming platforms, and enterprise environments. Observed attack traffic largely originates from Vietnam, Ukraine, Iran, Brazil, Kenya, and India, with Vietnam accounting for nearly half of the detected activity.
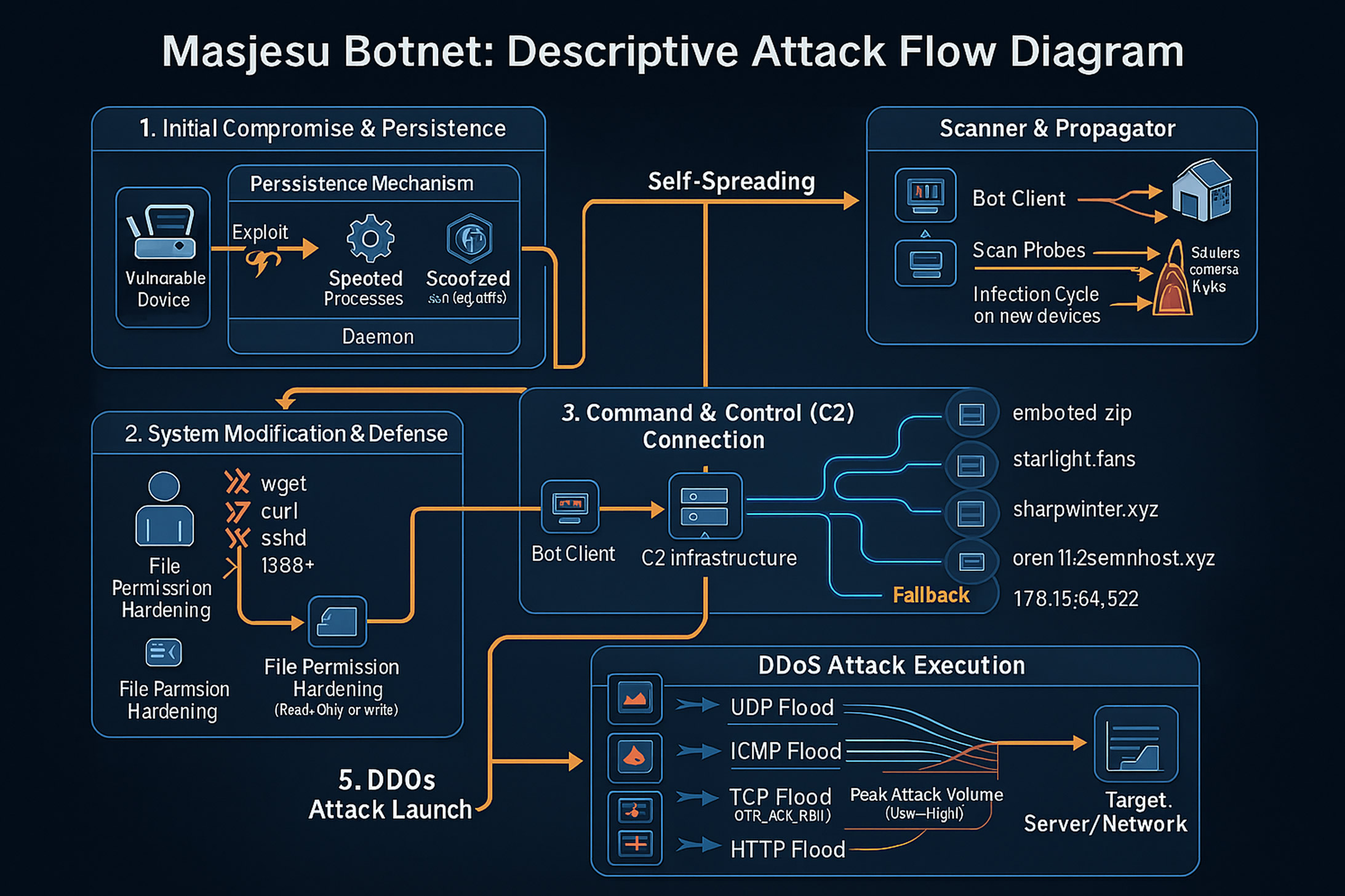
After infecting a device, the malware attempts to create and bind a socket on a hardcoded TCP port, 55988, allowing attackers to establish a direct connection. If this step fails, the malware immediately terminates the infection process.
When successful, the botnet establishes persistence, suppresses termination-related system signals, and halts commonly used utilities such as wget and curl possibly to prevent interference from competing malware. It then connects to an external command-and-control server to receive and execute DDoS instructions against designated targets.
Masjesu also incorporates self-propagation mechanisms, scanning random IP addresses for exposed services and assimilating newly compromised devices into its network. A notable addition to its exploitation arsenal is the targeting of Realtek-based routers by scanning port 52869, which is linked to the Realtek SDK’s miniigd daemon. This exploitation technique has previously been employed by other IoT botnets, including JenX and Satori.
“The botnet continues to broaden its reach by compromising IoT devices from a wide variety of manufacturers and architectures,” Trellix concluded. “Importantly, Masjesu appears to deliberately avoid high profile or sensitive organizations that could attract significant legal or law-enforcement scrutiny a tactic that likely enhances its long-term viability.”
Found this article interesting? Follow us on X(Twitter) ,Threads and FaceBook to read more exclusive content we post.


