Cybersecurity researchers have identified a new evolution of the Android malware family known as NGate, which now abuses a different legitimate application HandyPay to facilitate large‑scale NFC relay fraud. This marks a shift from earlier campaigns that relied on NFCGate or similar purpose‑built relay frameworks.
According to ESET, the threat actors behind the campaign obtained HandyPay an application designed to relay NFC data and modified it by injecting malicious code, rather than building an attack tool from scratch. The altered codebase appears to contain artifacts consistent with AI‑assisted or AI‑generated development, suggesting the attackers may have leveraged generative tools to accelerate malware creation.
“The attackers took a legitimate application that already supports NFC relay functionality and patched it with malicious code that appears to have been generated using AI,” said ESET researcher Lukáš Štefanko. “As with previous NGate campaigns, the malware enables attackers to relay NFC data from a victim’s payment card to an attacker‑controlled device, which can then be used for contactless ATM withdrawals and unauthorized transactions.”
In addition to relaying NFC data, the malicious payload is capable of capturing the victim’s payment card PIN and exfiltrating it to a command‑and‑control (C2) server, significantly increasing the impact and reliability of fraudulent cash‑out operations.
Background on NGate
NGate also tracked under the name NFSkate was first publicly documented by ESET in August 2024. At that time, researchers detailed its ability to perform NFC relay attacks, allowing criminals to intercept contactless payment data and use it remotely to carry out fraudulent transactions.
Roughly a year later, ThreatFabric, a Dutch mobile security firm, uncovered a related campaign dubbed RatOn, which used dropper applications impersonating adult‑themed versions of TikTok to distribute NGate. That campaign similarly focused on relaying NFC card data to enable real‑world financial fraud.
Brazil‑Focused Campaign
The latest iteration of NGate observed by ESET represents a notable shift in geographic targeting. For the first time, the malware has been seen primarily targeting users in Brazil, marking the country as the focus of a dedicated NGate campaign.
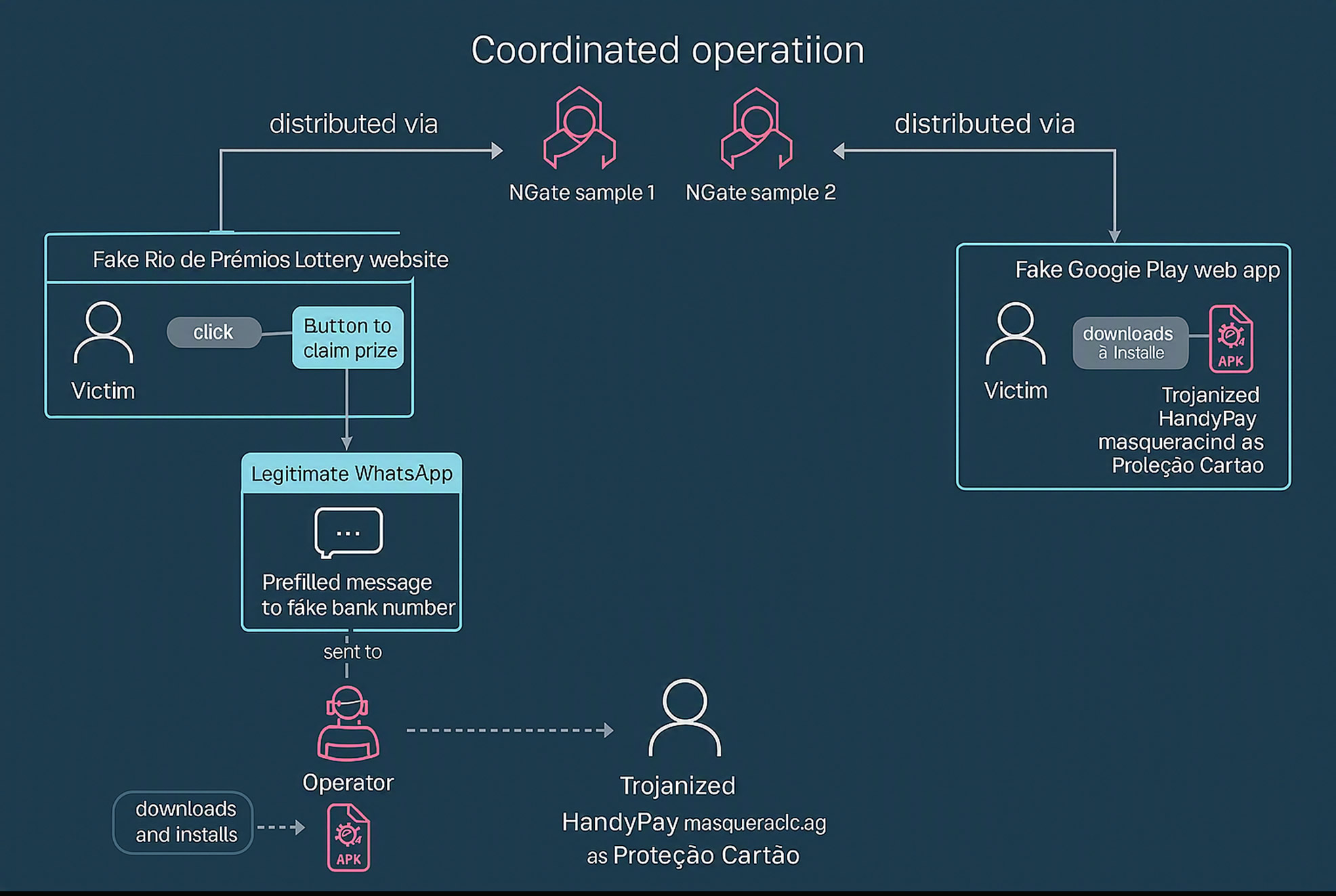
The trojanized version of HandyPay is distributed through several deceptive channels, including:
- Websites impersonating “Rio de Prêmios,” a well‑known lottery run by the Rio de Janeiro state lottery organization
- A fake Google Play listing masquerading as a card‑protection or security application
On the fraudulent lottery website, users are encouraged to click a button to claim a prize, which triggers a WhatsApp message flow. From there, victims are guided toward downloading the infected HandyPay application. Regardless of the delivery method, the malware prompts the user to set the app as the default payment application after installation.
Infection and Fraud Flow
Once installed and designated as the default payment app, the victim is instructed to:
- Enter their payment card PIN into the app
- Tap their physical card against the back of the NFC‑enabled smartphone
At this point, NGate abuses the underlying HandyPay functionality to capture and relay the NFC card data to the attacker’s device in real time. The attackers can then use the stolen data and PIN to perform contactless ATM withdrawals or initiate unauthorized payments.
ESET assesses that the active campaign likely began around November 2025. Importantly, the malicious version of HandyPay has never been published on the official Google Play Store, indicating that attackers rely entirely on social engineering and sideloading techniques to infect victims.
HandyPay has since launched an internal investigation to assess potential abuse of its application.
Cost and Stealth Advantages
ESET researchers noted that the campaign’s operators may have switched to HandyPay for economic and operational reasons. Compared to turnkey NFC fraud solutions some of which cost over $400 per month HandyPay’s lower subscription costs made it an attractive alternative.
“In addition to being cheaper, HandyPay does not request any dangerous Android permissions by default,” ESET explained. “It only needs to be set as the default payment app, which helps attackers avoid triggering suspicion or security warnings.”
Signs of AI‑Assisted Development
Analysis of the malicious application revealed unusual development artifacts, including the presence of emojis in debug output and toast messages a trait increasingly associated with large language model (LLM)‑generated code. While ESET cautioned that definitive attribution to generative AI is not possible, the evidence aligns with a wider industry trend.
Cybercriminals are increasingly using generative AI tools to write, modify, or obfuscate malware even when they possess limited programming expertise dramatically lowering the barrier to entry for complex financial fraud operations.
Broader Implications
“With the emergence of yet another NGate campaign, it is evident that NFC‑based fraud is accelerating,” ESET concluded. “This time, rather than relying on an established tool like NFCGate or malware‑as‑a‑service offerings, the attackers chose to trojanize HandyPay an application that already includes NFC relay capabilities.”
The campaign highlights a growing risk vector in mobile payments: legitimate NFC‑enabled applications can be covertly weaponized to conduct sophisticated fraud, especially when combined with convincing social engineering and AI‑assisted development.
Found this article interesting? Follow us on X(Twitter) ,Threads and FaceBook to read more exclusive content we post.


