Aeternum botnet leverages Polygon smart contracts for C2, complicating detection and takedown efforts.
Researchers at Qrator Labs have identified Aeternum, a botnet that operates its command-and-control (C2) through smart contracts on the Polygon blockchain. By decentralizing C2, the malware sidesteps conventional server-based disruptions, making it substantially harder to neutralize and increasing its durability and persistence in the wild.
As the Qrator Labs report explains, instead of traditional domains or servers for C2, Aeternum publishes instructions to the public Polygon network an ecosystem widely used by decentralized apps such as Polymarket, a major prediction market. This design renders Aeternum’s command infrastructure effectively permanent and resistant to standard takedown techniques.
Aeternum is a C++ botnet loader available in both 32‑bit and 64‑bit builds that uses Polygon as its C2 backbone. Operators write commands into Polygon smart contracts, while infected endpoints query public RPC endpoints, read on‑chain directives, and execute them.
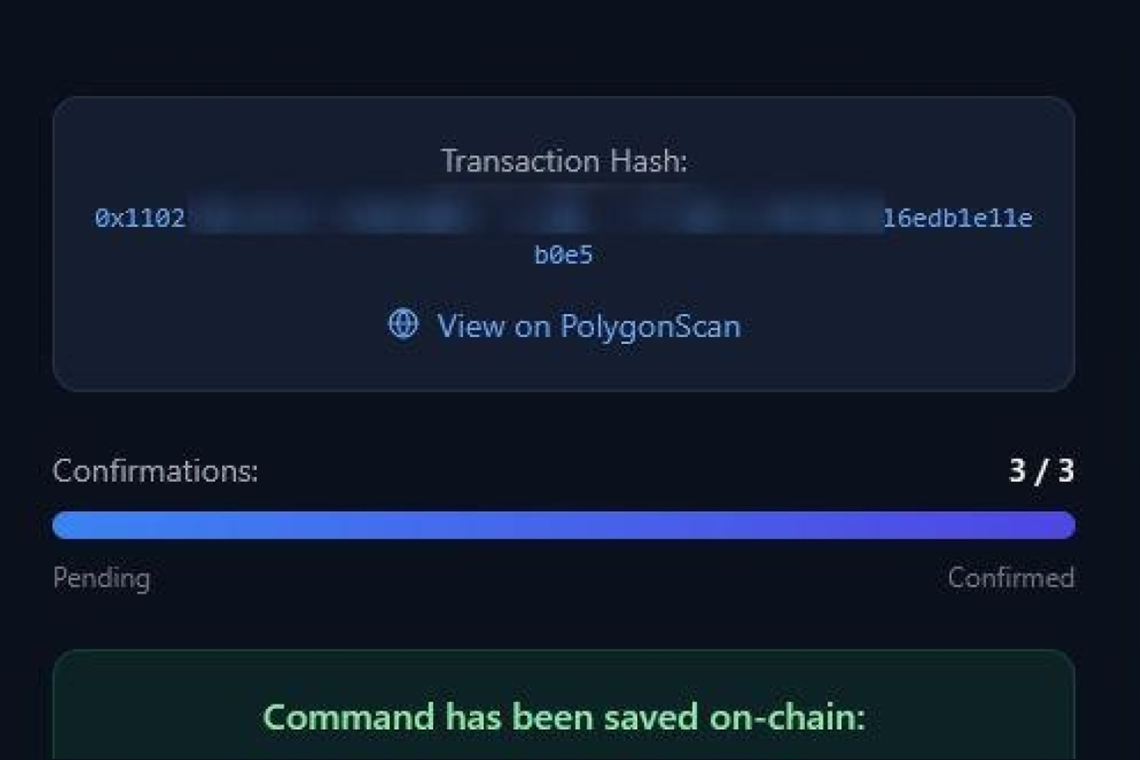
Through a web-based control panel, an operator selects a smart contract, chooses an action, attaches a payload URL, and broadcasts the command as a blockchain transaction. Once confirmed on-chain, the instruction becomes immutable and accessible to all infected hosts within minutes. Operators can juggle multiple contracts simultaneously, each tied to different payloads such as stealers, clippers, RATs, or miners. A built‑in ping capability also lets them monitor active infections and target systems precisely using hardware IDs and HTTP fingerprinting.
This blockchain-first C2 approach reshapes the takedown landscape. Traditional botnets depend on domains, IP addresses, or centralized servers that defenders can seize, suspend, or sinkhole. By contrast, Aeternum stores C2 on Polygon, replicated across thousands of nodes and reachable via numerous RPC gateways eliminating any single server that can be shut down. Whereas previous malware families like Glupteba treated blockchain as a fallback, Aeternum promotes it to the primary channel, removing many conventional disruption options.
Aeternum is marketed either as a lifetime package with a ready‑to‑use panel or as full C++ source code with updates. Operating expenses are minimal: roughly $1 in MATIC can cover 100+ blockchain command transactions. There’s no need for infrastructure like servers or domains just a crypto wallet and the control dashboard.
The malware further raises the bar with anti‑VM checks to evade sandboxing and a built‑in antivirus scan capability to test detections pre‑deployment, reducing friction for running a resilient and stealthy operation.
As the report notes, the seller includes a scantime AV scanner via the Kleenscan API, allowing operators to test builds against 37 antivirus engines before release. In shared screenshots, only 12 of 37 engines reportedly flag the sample, with several major vendors including CrowdStrike, Avast, Avira, and ClamAV showing “undetected.” These results reflect a single moment in time and will shift as vendors update signatures.
Even if Aeternum itself doesn’t see widespread adoption, blockchain‑based C2 has now emerged as a packaged underground capability. The model is effective, inexpensive, and likely to be reused and improved by other malware authors. Botnets built on this pattern could persist longer, scale bigger, and drive large‑scale operations such as DDoS, credential stuffing, click fraud, and proxy networks.
The report concludes that when C2 channels are immutable, traditional upstream interventions grow less effective. Even if every infected endpoint is cleaned, an operator can re‑activate the botnet using the same smart contracts without rebuilding infrastructure. As a result, proactive DDoS mitigation and edge‑level filtering become even more critical: if the source can’t be taken down, defenders must contain the impact at the perimeter.
Found this article interesting? Follow us on X(Twitter) ,Threads and FaceBook to read more exclusive content we post.